05 Sep 2022 Cryptojacking
News: According to a report by SonicWall, a US-based cybersecurity firm ‘Cryptojacking’ attacks on computer systems have gone up by 30% to 66.7 million in the first half of 2022 compared to the first half of last year.
GS Paper 3: Science and Technology- Developments and their Applications and Effects in Everyday Life; Awareness in the fields of IT, Space, Computers.

What is cryptojacking?
- Cryptojacking is a cyber attack wherein a computing device is hijacked and controlled by the attacker, and its resources are used to illicitly mine cryptocurrency.
- In most cases, the malicious programme is installed when the user clicks on an unsafe link, or visits an infected website — and unknowingly provides access to their Internet-connected device.
Why is cryptojacking done and how is it different from coin mining?
- Coin mining is a legitimate, competitive process used to release new crypto coins into circulation or to verify new transactions. It involves solving complex computational problems to generate blocks of verified transactions that get added to the blockchain. The reward for the first miner who successfully manages to update the crypto ledger through this route is crypto coins.
- But the race to crack this 64-digit hexadecimal number code needs considerable computing power involving state-of-the-art hardware, and electrical power to keep the systems involved up and running.
- Cryptojackers co-opt devices, servers, and cloud infrastructure, and use their resources for mining. The use of ‘stolen’ or cryptojacked resources slashes the cost involved in mining.
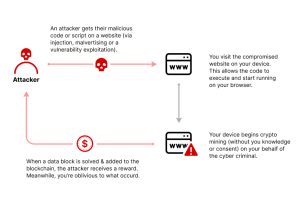
Image Courtesy: Imperva
What are the main methods that cryptojackers use to maliciously mine for cryptocurrencies?
- File-Based Cryptojacking: With file-based cryptojacking, malware is downloaded and runs an executable file that spreads a cryptomining script throughout the IT infrastructure. One of the most common ways that cryptojacking occurs is by using malicious emails. An email is sent containing an attachment or link that looks legitimate. When a user clicks on the attachment or link, code is executed that downloads the cryptomining script onto the computer. This script works in the background without the user’s knowledge.
- Browser-Based Cryptojacking: Cryptojacking attacks can take place directly within a web browser, using IT infrastructure to mine for cryptocurrency. Hackers create a cryptomining script using a programming language and then embed that script into numerous websites. The script is run automatically, with code being downloaded onto the users’ computer. These malicious scripts can be embedded in ads and vulnerable and out of date WordPress plugins. Cryptojacking can also happen through a supply chain attack, where cryptomining code compromises JavaScript libraries.
- Cloud Cryptojacking: When hackers use cloud cryptojacking, they search through an organization’s files and code for Application Programming Interface(API) keys to access their cloud services. Once access is gained, hackers siphon unlimited CPU resources for cryptomining, resulting in a huge increase in account costs. Using this method, hackers can significantly accelerate their efforts of cryptojacking to illicitly mine for currency.
Image Credit: Varonis
How does Cryptojacking Work?
- Compromise an Asset to Embed Script: Cyberhackers, also known as threat actors, compromise an asset by embedding cryptomining code using one of the three methods above.
- Execute Cryptomining Script: Once embedded, cryptojackers are counting on victims to execute the script. Users either click on an attachment or link to execute and run the cryptomining script or browse to a website with infected ads.
- Cryptomining Begins: After being executed, the cryptomining script runs in background, without the knowledge of the user.
- Solving Algorithms: The script uses computer power to solve complex algorithms to mine what is called a “block.” These blocks are added to a blockchain, the technology which stores digital information about cryptocurrency.
- Jackers Receive a Cryptocurrency Reward: Each time a hacker adds a new block to the chain they receive cryptocurrency coins. Without very little work or risk, these threat actors are able to gain reward in cryptocurrency that they can anonymously put directly into their digital wallets.
How to detect cryptojacking?
- Be aware of decrease in performance in computing devices.
- Look for overheating of devices and running fans for cooling.
- Monitor computer for an increase in CPU usage.
- Check for coding and file changes on your site.
- Scan for malware to monitor your websites.
- Follow crypto news and look for parallels on your site.
What are the signs that a device is attacked by cryptojacking?
- Device slowing down.
- Device heating up.
- Battery of the device drained faster than usual.
Why have cryptojacking incidents gone up?
- Crackdown on ransomware attacks by agencies is forcing cybercriminals to look for alternative methods.
- Cryptojacking involves lower risk, and promises potentially higher payday.
- Cryptojacking is hard to detect and the victims of these attacks mostly remain unaware that their systems have been compromised.
- Unlike ransomware which announces its presence and relies heavily on communication, cryptojacking has a lower potential of being detected by the victims, as cryptojacking can succeed without the victim ever being aware of it.
- It’s hard to tie cryptojacking to criminal activity: As unsuspecting users across the world see their devices get unaccountably slower, but it’s hard to tie it to criminal activity, much less point to the source.
Why should this be a concern?
- Large number of individuals and businesses are on the target list of cryptojackers.
- According to the report, cryptojacking incidents targeting the retail industry rose by 63% year-to-date, while similar attacks on the financial industry skyrocketed 269%.
- According to Interpol the primary impact of cryptojacking is performance-related, though it can also increase costs for the individuals and businesses affected because coin mining uses high levels of electricity and computing power.
How to Prevent Cryptojacking?
- Train professions to detect cryptojacking.
- Not to click on links on emails.
- Use Anti-Cryptomining Extensions.
- Use Ad-Blockers to block malicious code in online ads.
Sources: Indian Express; Varonis
Source Links:
- Indian Express: https://bit.ly/3DaM1l4
- Varonis: https://bit.ly/3Qx7Lea
Yojna IAS Daily current affairs eng med 5th Sep

No Comments