29 Jan 2024 End – to – End Encryption and Right to privacy
Source – The Hindu and PIB.
General Studies – Paper 3 – Protection of Privacy, Fundamental Rights, Information Technology and Computers, Data Security, Data Protection Laws, Advantages and Disadvantages of End-to-End Encryption.
Why in the News ?

- On the one hand, in the context of compliance with India’s proposed Online Security Bill (OSB) for the entire country, the head of WhatsApp has said that – “WhatsApp will not comply with India’s Online Security Bill (OSB), which effectively Prohibits “end-to-end (E2E) encryption.” Apple has announced that – “It will further increase the data points protected by end-to-end encryption (E2EE) on iCloud from 14 to 23 categories, as a result of which the protection of consumers’ privacy can be ensured. “
Main objectives of sharing data – breach – research :
- According to a recent survey-research conducted by Apple, which is also called data-breach-research, the total number of data breaches in India from the year 2013 to the year 2021 is three. Has increased more than times. Only in the year 2021 . In this year alone, data of 1.1 billion personal records has been revealed.
- With this end-to-end encryption, even if someone’s personal data is breached in the cloud, the user’s data will remain completely safe. This additional layer/level of encryption will somehow prove to be extremely valuable from the right to privacy and security of personal data point of view to deal with the hacking attacks launched by some funded groups and also from data theft and other security point of view.
What is Encryption ?
- One way to protect data from unauthorized access or tampering is called encryption. This process involves converting data into a secret code that only the intended recipient can understand. It is useful for various cases. Such as securing mutual online communications, storing sensitive information among themselves and verifying their digital identities, etc.
There are mainly two types of encryption-
-
symmetrical and
-
Asymmetric.
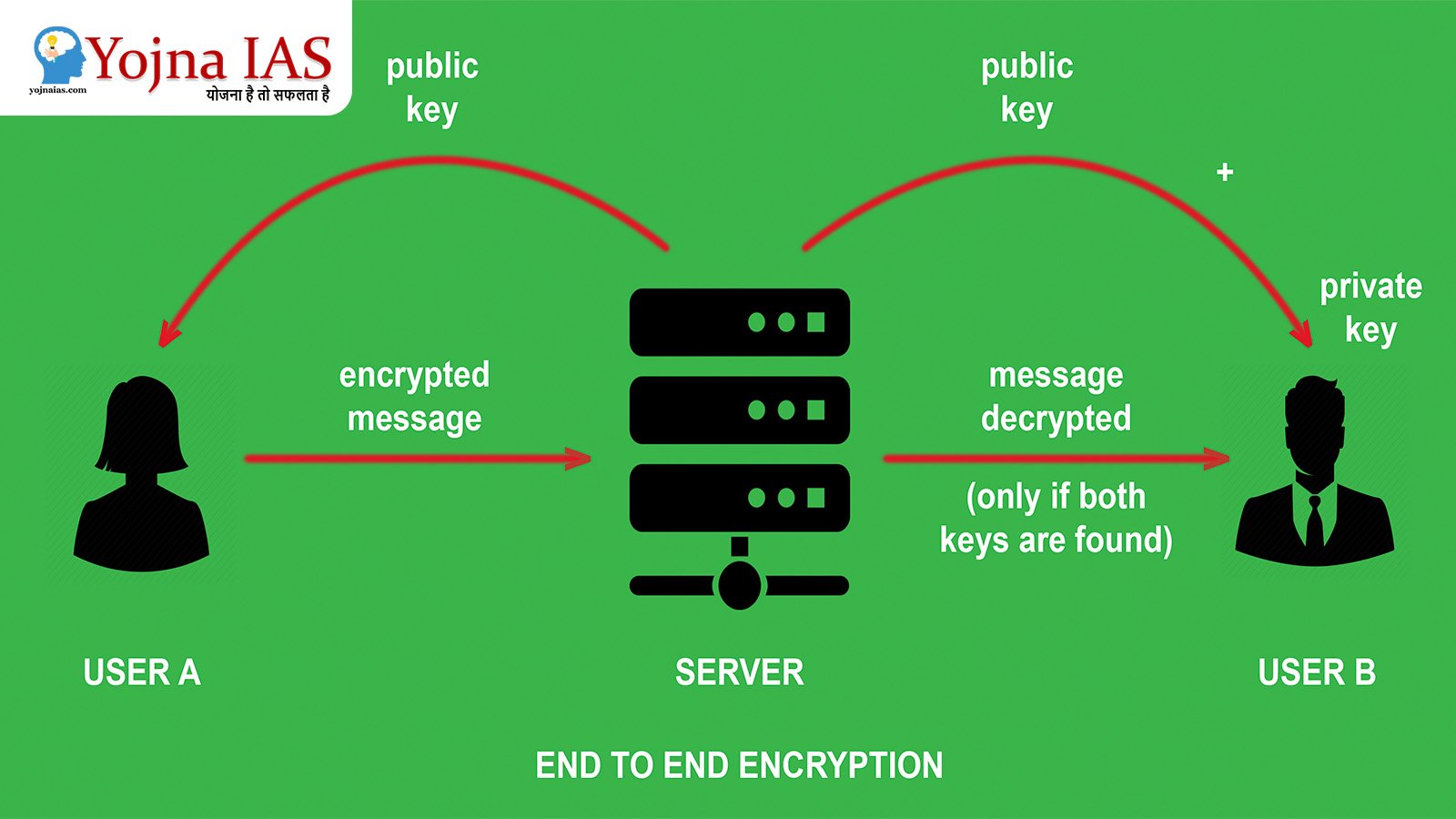
- Symmetric encryption uses a single key to encrypt and decrypt data, while asymmetric encryption uses a pair of keys – one public and one private. One thing to note is that any public key can be shared with anyone, but in asymmetric encryption the private key is always kept secret.
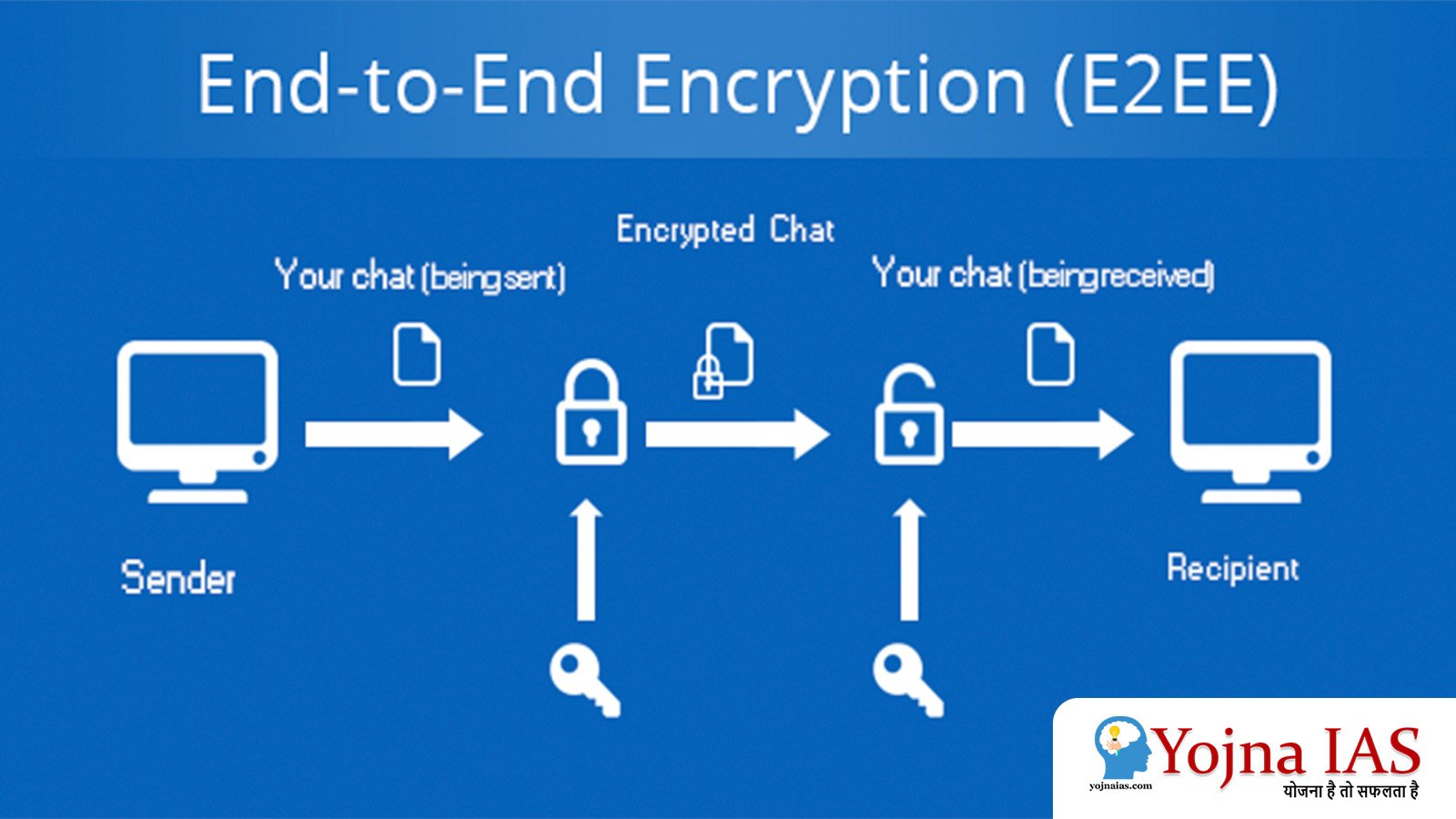
Working mechanism of end-to-end encryption :
- Any end-to-end encryption relies on an elegant but complex cryptographic system to protect the data in transit or shared between two devices. The key element is asymmetric cryptography, which uses pairs of keys – public and private – to secure communications. The public key encrypts the data, while the private key decrypts it.
- It is a communication process that encrypts the data being shared between two devices.
- This prevents third parties such as Internet Service Providers (ISPs), cloud service providers and cyber criminals from accessing the data, especially when one’s personal data is being transferred.
Mechanisms used in End- to- End Encryption :
- Cryptographic keys used to encrypt and decrypt messages are stored on endpoints.
- The process of end-to-end encryption uses an algorithm that converts standard text into an unreadable format.
- This format can only be opened or read by people with decryption keys, which are stored only on the endpoints and are not shared with any third parties, including service providing companies.
Usefulness of end-to-end encryption in mutual communication :
- End-to-end encryption has long been commonly used in India when transferring business documents, financial statements, legal proceedings and personal conversations.
- It can also be used to control the authorization of users when accessing any stored data.
- End-to-end encryption is used to secure user-to-user communications.
- It is commonly used to secure any passwords, ensure the security of stored data, and also for provisional protection of data security on cloud storage.
British Online Security Bill :
- The Online Safety Bill (OSB) is a British proposed legislation to impose ‘duty of care’ obligations on online platforms to improve online safety. Whose work is motivated by forcing Internet service providers to work to improve online security.
- Section 110 of the Terrorism and Child Sexual Exploitation and Abuse (CSEA) Content Identification and Online Safety Bill (OSB) empowers the regulator to issue notices to most internet service providers, including private messaging apps, to prevent terrorism and Child Sexual Exploitation and Abuse (CSEA) can be investigated and immediately removed from internet platforms.
- The Online Security Bill (OSB) does not mandate the removal of end-to-end encryption but would require any messaging app to scan all messages to flag such content, which would actually mean removing security mechanisms such as encryption. To break.
- The Online Security Bill (OSB) is seen as contradictory to the fundamental rights of an individual such as privacy and freedom of expression which allow states or governments to restrict and monitor the individual’s fundamental rights such as privacy and freedom of expression.
Online Security Bill (OSB) in India :
Information Technology Act 2000 :
- This Act brought by the Government of India regulates and guides the electronic and wireless modes of communication in the country. It exempts us from making any concrete provision related to encryption or making any strict policy at the concrete level, which makes this Act a matter of concern from the point of view of the question of privacy of consumers and it is a major step forward in the field of information and technology in India. Also demands making a concrete guideline.
Digital Media Code of Conduct – Rules 2021 :
- Through what is commonly called traceability, the Government of India has made it mandatory for messaging platforms with more than five million users in India to ‘enable the identification of the first originator’ of the message. The Government of India has mandated this through the Information Technology (Intermediary Guidelines and Digital Media Ethics Code) Rules, 2021.
- This information about the person who first sent the message, the number of times he has sent a message and the number of times he has forwarded it is also contained in this Code of Conduct rule.
- WhatsApp’s penetration rate in India is over 97%, while in the United Kingdom it is around 75%. Because there are 487.5 million WhatsApp users in India where the messaging platform accounts for 22% i.e. 2.24 billion monthly active users.
Benefits of End-to-End Encryption (E2EE) :
End-to-end encryption helps in providing security in mutual communication :
- End-to-end encryption helps provide security in communications because end-to-end encryption uses public key cryptography, which stores the private key on endpoint devices. Messages can only be decrypted using these keys, so only people with access to the endpoint device are able to read the message.
Helpful in keeping safe from third parties :
- End-to-end encryption (E2EE) also serves to ensure that consumers or users are protected from malicious parties, including Internet data service providers, cloud storage providers, and companies that handle encrypted data.
It is free from any kind of interference :
- The decryption key does not need to be provided with E2EE as it is already available to the recipient.
- If a message encrypted with the public key is tampered with during transmission, the recipient will not be able to decrypt it and will not be able to access the tampered content.
Unreadable and forced to comply with government regulations :
- Many industries are bound by regulatory laws/requirements or compliance laws that require encryption-level data protection as a primary requirement. So end-to-end encryption (E2EE) can help organizations keep data secure by making it unreadable.
Disadvantages of End- to- End Encryption (E2EE) :
It is extremely complex to define endpoints :
- Some end-to-end encryption (E2EE) implementations in India allow encrypted data to be encrypted and re-encrypted at certain points during transmission.
- In this it clearly defines and differentiates the endpoints of the communication circuit. If the endpoints are compromised in any way, the encrypted data may be exposed. Therefore, it is extremely complex to define the endpoints of a communication circuit.
Excessive provision of confidentiality :
- Governments and government law enforcement agencies have always expressed concern that end-to-end encryption (E2EE) can protect people sharing illegal content because service providers are unable to provide access to the content to law enforcement.
Lack of protection for metadata and facilitating data misuse :
- In any type of mutual communication, messages are encrypted, information related to the message such as date of message and sender’s information etc. is visible even after sending the message, making it vulnerable to those who misuse the data in any way. It may prove helpful.
The legal framework currently in place in India for End-to-End Encryption (E2EE) :
Currently, India lacks any specific legislation related to End- to- End Encryption (E2EE) :
- At present, there is no specific law regarding end-to-end encryption (E2EE) in India. Although many industry standards governing the banking, finance, and telecommunications industries include minimum encryption standards that are used to protect mutual transactions, these are limited to certain specific sectors and are not easily accessible to common consumers. Unable to access.
Restrictions on End- to- End Encryption (E2EE) technologies :
- Currently, as per the terms of the licensing agreement between ISPs and DoT in India, consumers or users are not allowed to use encryption standards larger than 40 bits using symmetric key algorithms or comparable methods without prior approval. , while in India itself there are several additional rules and recommendations that allow the use of encryption levels higher than 40 bits for specific regions of India.
Conclusion: / Solution path :
- Through the Information Technology in India (Intermediary Guidelines and Digital Media Ethics Code) Rules, 2021, the Government of India seeks to encourage self-regulation of these social messaging platforms while protecting the right of individuals to privacy and freedom of expression. It keeps and guides these messaging platforms keeping in mind the privacy of the consumers, but still there are some criticisms which draw our attention towards government regulation in this regard as it is related to the issue of individual privacy. Lives. Only by finding a solution to this, the concept of India as a democratic and public welfare state can be confirmed.
IT rules do not follow human rights conventions :
- India’s new information technology (IT) rules violate the International Covenant on Civil and Political Rights (ICCPR) under the Human Rights Convention. Article 19(3) of the ICCPR provides for freedom of speech and expression. Which is for national security and public opinion or public health and morality. It is being said that all these things are being stopped due to the new IT rules.
The government will manage the data of common users :
- Despite there being a freedom of expression law in India, Special Messengers Company says that the government is monitoring the company and rapidly removing user generated content. This violates the right to freedom of expression in India. Common citizens of India have expressed concern that a system is being prepared to remove content from digital platforms. Due to which those working between consumers and the company can take advantage of it.
The main reason for the dispute between the Government of India and WhatsApp :
- There is an ongoing dispute between the Government of India and WhatsApp regarding the end-to-end encryption (E2EE) technology of WhatsApp. Last month, WhatsApp had opposed the IT rule. It was alleged that consumers’ right to privacy is in danger. The UN has been supporting end-to-end encryption (E2EE) since its inception. They believe that this is an effective technical safeguard. This protects the right to privacy.
Government collects data to protect the unity and integrity of India and to prevent communal riots/violence :
- When any violence or messages harming the unity and integrity of India go viral. It is used when a woman is being portrayed in a compromising position or in an inappropriate manner or when sexual issues related to children have to be explored. So who has spread the message and for what purpose can be found out.
- There is tension between WhatsApp and the Government of India regarding the rule of traceability. End-to-end encryption is designed to protect the privacy of users. The government’s argument is that if they get to read the messages of all the users, they will easily detect the person spreading rumors on social media and prevent any kind of communal riots or violence while implementing measures to safeguard the unity and integrity of India. Can be stopped.
Download Yojna daily current affairs eng med 29th Jan 2024
Practice Questions for Preliminary Exam :
Q.1. Consider the following statements regarding the Online Security Bill (OSB) in India.
- The Online Safety Bill (OSB) is a British proposed legislation to impose ‘duty of care’ obligations on online platforms to improve online safety.
- Section 110 of the Terrorism and Child Sexual Exploitation and Abuse (CSEA) Content Identification and Online Security Bill (OSB) empowers the regulator to issue notices to most internet service providers.
- Through traceability, the Government of India has made it mandatory for messaging platforms with more than five million users in India to ‘enable the identification of the first originator’ of a message.
- There are four types of end-to-end encryption.
Which of the above statement /statements is correct?
(A) Only 1, 2 and 4
(B) Only 2, 3 and 4
( C ) Only 2 and 4
(D) Only 1, 2 and 3
Answer – (D).
Practice Questions for Main Exam :
Q.1 How do the current online security bill in India and the individual’s right to privacy and expression contradict each other ? Give a logical explanation.
Qualified Preliminary and Main Examination ( Written ) and Shortlisted for Personality Test (INTERVIEW) three times Of UPSC CIVIL SERVICES EXAMINATION in the year of 2017, 2018 and 2020. Shortlisted for Personality Test (INTERVIEW) of 64th and 67th BPSC CIVIL SERVICES EXAMINATION.
M. A M. Phil and Ph. D From (SLL & CS) JAWAHARLAL NEHRU UNIVERSITY, NEW DELHI.

No Comments